We're Here To
Help

ISO 27001:2022 is the internationally recognised standard for Information Security Management Systems (ISMS). It provides a structured framework for identifying, managing and reducing risks to sensitive information across your organisation.
For organisations handling client data, financial information, intellectual property or regulated assets, ISO 27001 certification provides independent assurance of effective information security governance, enabling you to satisfy enterprise due diligence and strengthen your competitive position.
We provide specialist ISO 27001:2022 certification consultancy and support.
Whether guided implementation, co-delivered support or full-service ISMS development is required, we prepare organisations for independent certification, aligning operational practice with audit requirements.
ISO/IEC 27001:2022 is the global standard for establishing and maintaining an Information Security Management System (ISMS).
It is a risk-based management system requiring organisations to define scope, assess and treat information security risks, implement appropriate controls and maintain continual oversight through internal audit and review.
Certification is awarded following independent assessment by a UKAS-accredited certification body, confirming that your ISMS meets the requirements of ISO/IEC 27001.
The 2022 revision refined control structures, reduced duplication and reorganised Annex A into four domains: organisational, people, physical and technological controls. We support both first-time certification and transition to ISO 27001:2022 where required.
In many sectors, ISO 27001 has shifted from competitive advantage to contractual expectation.
Increasingly, it is a prerequisite for securing major contracts, satisfying procurement due diligence and strengthening competitive position.
ISO 27001 certification is built around two core components: a structured management system and risk-based control implementation.
Our role is not to implement every control by default, but to ensure your ISMS is proportionate, defensible and aligned to operational reality, built to withstand independent audit.
To ensure information security is governed at a strategic level, not confined to a standalone IT function, the standard requires your organisation to demonstrate:
- Clearly defined scope and organisational context
- Senior leadership accountability for information security
- A documented and repeatable risk assessment methodology
- Risk treatment decisions aligned to business objectives
- Competence, awareness and communication controls
- Ongoing internal audit and management review
- Corrective action and continual improvement mechanisms
Control selection is risk-based and must be formally justified within a Statement of Applicability (SoA), supported by a maintained risk register and treatment plan. The 2022 revision includes 93 controls across four domains:
- Organisational
- People
- Physical
- Technological
Achieving ISO 27001 certification requires more than documentation. It demands a structured, functioning ISMS supported by leadership oversight, internal audit and demonstrable risk control.
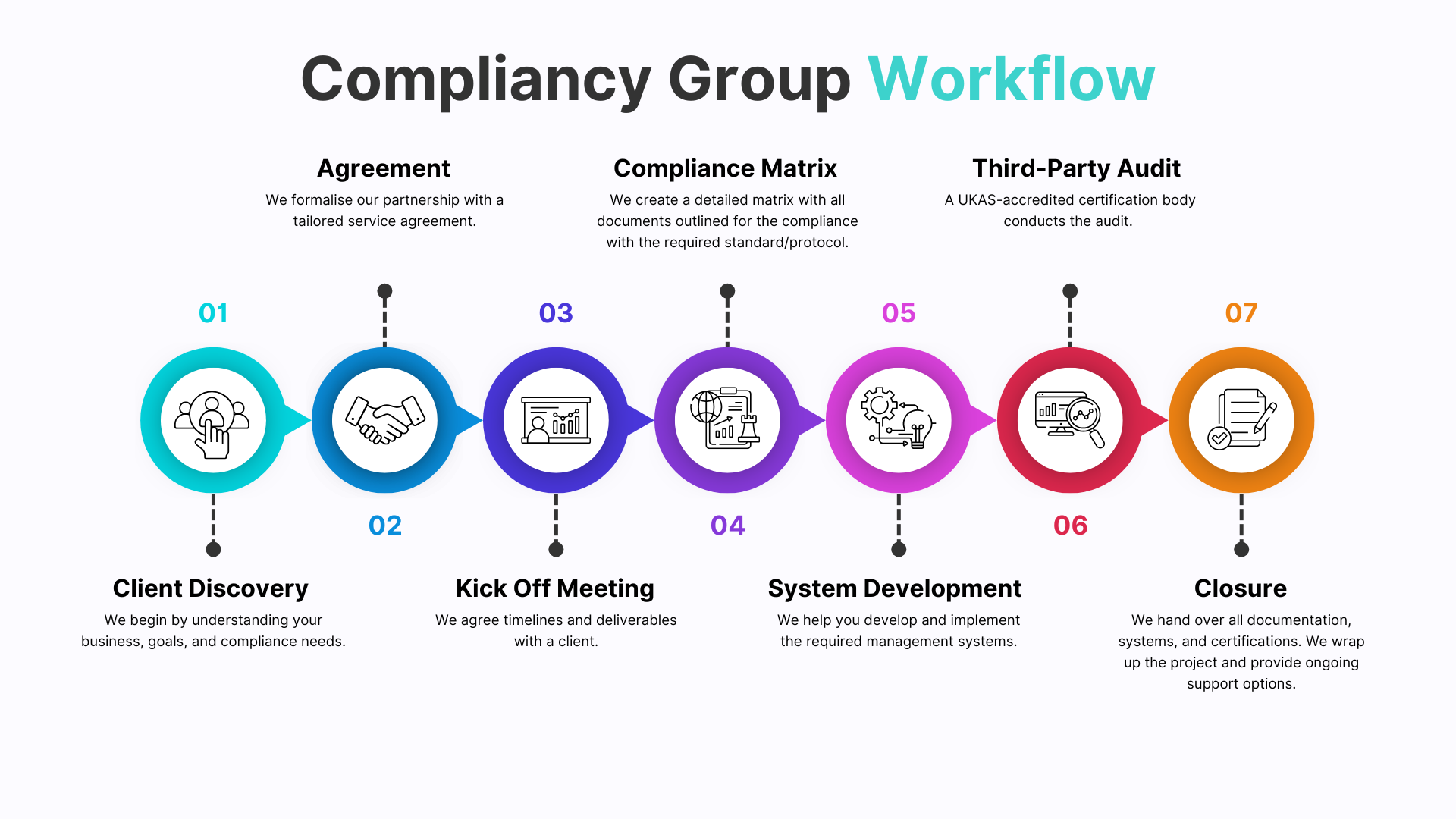
We lead you through the full certification pathway: designing and embedding your ISMS, structuring risk assessment and treatment, conducting internal audit and management review, and preparing for independent assessment by a UKAS-accredited certification body.
We ensure your systems, documentation and personnel are fully prepared before external audit begins, minimising nonconformities and supporting a controlled, confident route to certification.
Consultancy delivered by experienced ISO and governance professionals who understand both the technical requirements of the standard and the commercial context behind risk decisions.
Direct consultant involvement providing structured leadership oversight, governance alignment and defensible decision-making throughout your certification journey.
Control frameworks tailored to your operational model, supported by clear Statements of Applicability and structured, audit-ready evidence.
Preparation structured around UKAS-accredited certification body expectations, ensuring readiness for both Stage 1 and Stage 2 independent audit.
We adapt our role to your operational complexity. Our involvement scales to your internal capability, from structured mentoring and co-delivered ISMS development to full-service implementation and independent internal audit readiness.
Continued involvement beyond certification to maintain standards, prepare for surveillance audits and strengthen long-term governance maturity.





Our specialist team are here to help you through every stage of the certification process.
ISO/IEC 27001 is the international standard for information security management, providing a framework for establishing, implementing, and improving an Information Security Management System (ISMS).
The three key elements are confidentiality, integrity, and availability of data.
Organisations must identify, assess, and treat information security risks, and implement appropriate security controls to mitigate those risks.
The six areas are security policy, asset management, physical and environmental security, access control, incident management, and regulatory compliance.
Annex A divides the 93 controls into four categories: organisational, people, physical, and technological.
Establish and implement an ISMS, conduct a risk assessment, apply security controls, document processes, and undergo audits by an accredited certification body.
Clause 4: Context of the Organisation Clause 5: Leadership Clause 6: Planning Clause 7: Support Clause 8: Operation Clause 9: Performance Evaluation Clause 10: Improvement
Certification typically takes 3 to 12 months, depending on company size and ISMS complexity.
It helps organisations proactively manage cyber risks and demonstrate a strong commitment to information security.